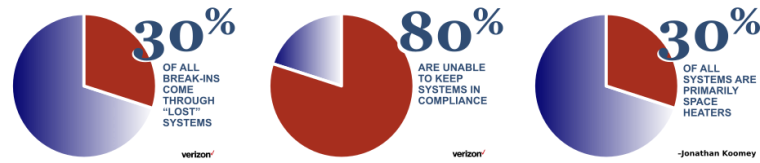
Securing your systems is a daunting task – it feels like eating an elephant. When compared to hardening guidelines like the DISA/NIST STIGs, a single out-of-the-box system can have a hundred or more issues. When you multiply that by a large number of systems, despair and paralysis can easily set in. This article (fifteen minutes to better security) is first in a series which outline a process for efficiently measuring, triaging, and managing your journey towards a better security posture for your servers.
No matter your threat model, you need to understand what you have (“know yourself”). We help you begin this journey with activities which will teach you a surprising amount about your current status and the work ahead of you in 15 minutes. This article is not designed to teach you about security – I assume you know why you want to secure your servers, and have general background on system hardening.