In lots of ways, the most dangerous attack any enterprise sustains comes one way or another through “social engineering”. The reason why this works so well is that it’s mainly an application of social skills – the kind people use everyday to work together and get things done every day. Like any tool, skill, or weapon, it can be used for good or for evil.
This came to mind when I was recounting a story from years ago to my friend Emily Ratliff – and she laughed and said “that’s social engineering” – and I suppose she’s right. So this week, I’ll tell the story of my tiny bit of social engineering that snagged me a cool and unique book.
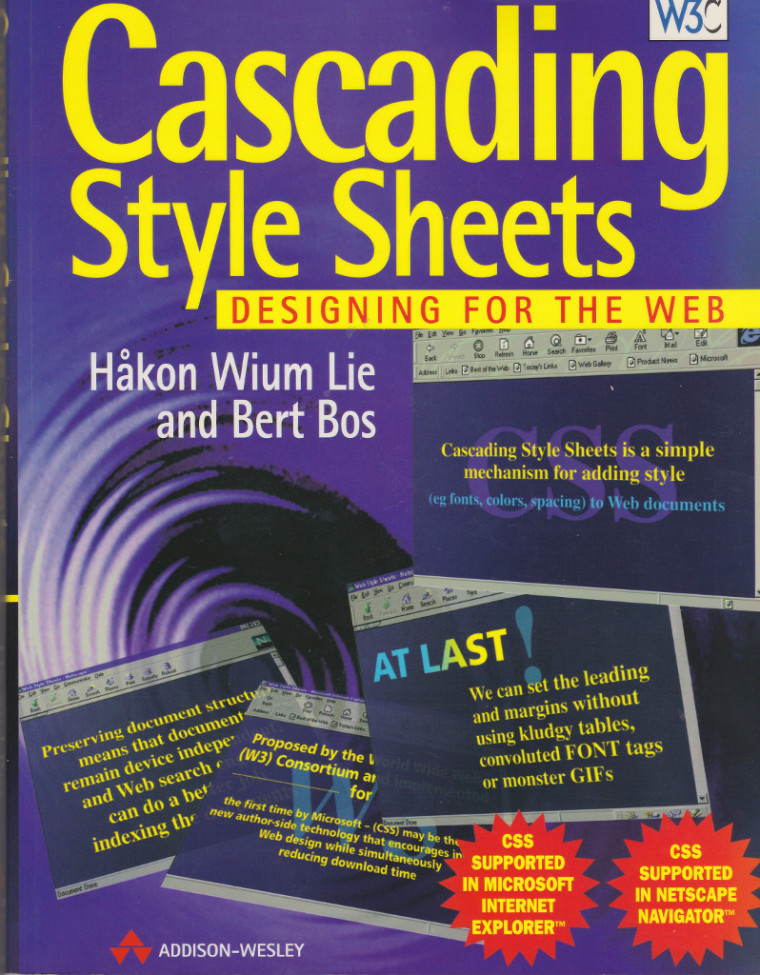
Back in April of 1997, I was attending the WWW6 world wide web conference at Santa Clara. It was an exciting time for the Web, there was this revolutionary new development in the web – Cascading Style Sheets that was set to replace all the old table cruft and monster GIF images that webmasters had used to customize layout. And indeed, it was very powerful, and survives to this day as a key part of our web experience.
The authors of this specification were two guys – Håkon Wium Lie and Bert Bos. I had seen both of their pictures, and Håkon’s had very distinctive skinny glasses that gave him a unique look. What I didn’t know is that the two of them had come out with a book on the topic.
Is it Social Skills – or Social Engineering?
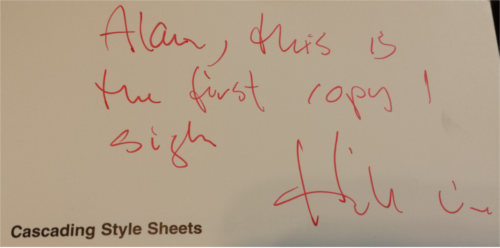
I went to a number of sessions which I enjoyed – all forgotten by now. But what I do remember quite clearly to this day is looking up from the ground floor to the mezzanine and seeing this person at the top of the escalator. When I looked carefully, I recognized him as Håkon Wium Lie. He was standing next to a box and another person who had handed him a book, which he was looking over and smiling about. The person with the box and the book was wearing a suit, which put him out of place in such a geeky conference. I realized it looked a lot like this person was his publisher, and he was looking over a book – and I guessed it was a book that Håkon had authored. So I got on the escalator and said “So, is this your new book?”. He said, “Yes, would you like a copy?”. Naturally I said yes, and he gave me a copy, which he signed like this: “Alan – this is the first copy – Signed Håkon Lie”.
Why did Emily call this social engineering? Well, I saw a potential opportunity, recognized it for what it likely was, gave information which wasn’t full disclosure – I didn’t know he’d written a book, and I didn’t know what it was about, but I went boldly on – pretending that I did. While ascending the escalator, I thought about what I’d say that would make him likely to give me a copy, and received a prize as a result of my willingness to captialize on the opportunity. This was all using basic social skills – being vague, getting feedback on the situation, and proceeding just like I’d known all along. These are exactly the same kinds of methods attackers use against us. The difference here was he wanted to give the book away, and what I did helped him accomplish his goals – as well as scoring a cool book with a unique signature in it.
Although the Assimilation System Management Suite can’t directly protect against social engineering, its cybersecurity features can help you discover the results of intruders in your infrastructure, and make it harder for them to get in using other methods.

Please note: I reserve the right to delete comments that are offensive or off-topic.