Tag Archives: compliance
How the right CMDB can improve your security posture

In a couple of earlier blog posts, I wrote an article about what characteristics would make a CMDB suitable for a “modern” DevOps-like environment. The first article talked about what characteristics one would like in such a CMDB. The second article evaluated the Assimilation Suite in terms of those characteristics. This article discusses how a CMDB can improve your security posture.
In today’s blog post, I’d like to do something similar – but looking at a CMDB from a security perspective. That is, this blog post is the first part of a discussion of what a security-oriented CMDB ought to look like and how it can improve your security posture.
Assimilation Versus Orchestration Tools Like Chef or Puppet?
Assimilation 2016 Security Roadmap

About a year ago, we created a security roadmap for the Assimilation Project. It’s time to update it and see how we’ve progressed since then – hence our Assimilation 2016 Security Roadmap. The Assimilation Security software concentrates on low-noise automated security tools. We expect to enhance our capabilities in best practice analyses, checksum integrity analyses, patch […]
System Management Survey

If you manage, secure, or plan for IT environments or DevOps, we’d love for you to take our System Management survey. Right now, we’re busy planning on how to make the Assimilation Suite better in 2016. Your responses will be a huge help in giving us a sharp focus on how best to improve IT management for you and others in the IT community. If you can help us out, we’ll send you a small token of our appreciation
Eating the Security Compliance Elephant
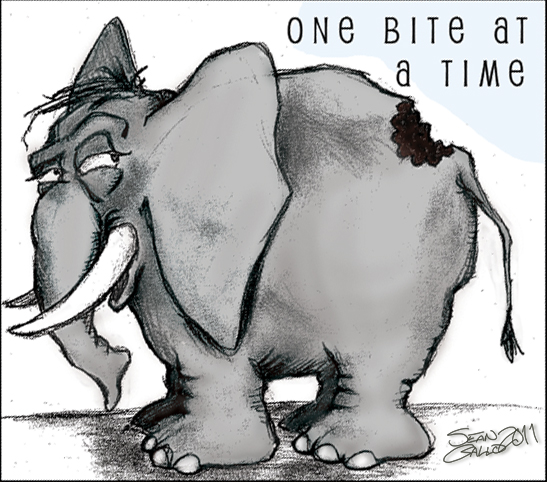
Getting your organization into security compliance is a lot like eating an elephant. It’s a daunting task, but there’s really not much you can do but eat it one bite at a time. A recent Verizon survey indicated that 80% of all organizations surveyed indicated they have trouble staying in compliance. For these organizations, they get to eat that elephant again and again – and worse yet, under the critical eye of an auditor. Once you eaten the elephant, you don’t want it to become an annual event.


