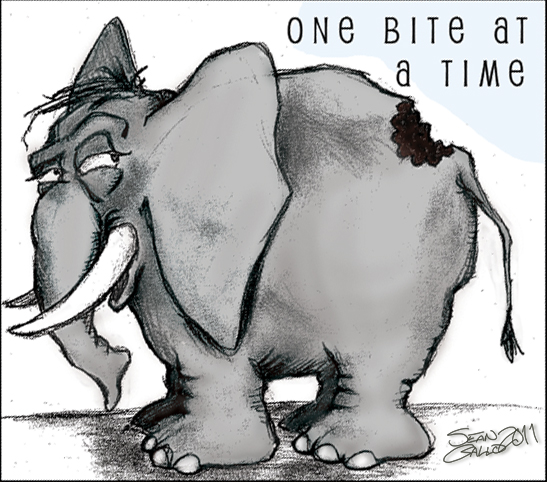
Getting your organization into security compliance is a lot like eating an elephant. It’s a daunting task, but there’s really not much you can do but eat it one bite at a time – although there are things you can do to make that initial process more palatable. A recent Verizon survey indicated that 80% of all organizations surveyed indicated they have trouble staying in compliance. For these organizations, they get to eat that elephant again and again – and worse yet, under the critical eye of an auditor.
This is a painful reality for many organizations. Once you eaten the elephant, you don’t want it to become an annual event.
Once you’ve eaten the elephant, you don’t want it to become an annual event.
In larger organizations, there are lots of reasons why this can happen, but surely one of the most common is that the people who bring systems out of compliance didn’t realize they’d caused a problem. Security rules are often complex, difficult to communicate, and staff is always changing. By the time the mistake is discovered, memories are dim, staff has moved on, and time is short. In such an environment, it’s hard to ensure that the entire organization is aware of all the different jots and tittles (details) of the security best practice hardening rules. Not only is the organization fluid over time, but so are security rules. Given all this, it’s no wonder that so many organizations have trouble staying in compliance.
Avoid Continual Indigestion: Eat The Elephant Once
What’s needed is a way to automatically ensure that systems and services are continually in compliance, and when they aren’t, notifications or alerts happen immediately. When issues are discovered as they’re created, these mistakes become teachable moments, which are far more effective than an audit issue coming up 10 months later. In addition, the problems can get solved in hours or days, drastically reducing the chances of attackers exploiting these vulnerabilities. After all, the point of all these rules is to keep attackers at bay.
Given the ever-growing shortage of security professionals (not to count their cost), it’s pretty clear that you can’t solve this problem by throwing more people at the problem. What’s needed is a low-overhead, automated way of ensuring compliance with your organization’s security best practice rules.
There are really two parts to this problem:
- A tool which can alert on violation of best practices in minutes.
- A set of best practices.
The Assimilation System Management Suite is currently adding monitoring of best practices to its repertoire, as our next major feature. This extreme-scale suite is ideally suited for this task, because it already discovers security settings on systems, and it is incrementally notified when they change – allowing it to easily evaluate a particular system hardening rule exactly and only when the underlying data changes. It will then generate an alert when something goes out of compliance and extinguish it when it comes back into compliance. As a monitoring system, it is already in the business of generating alerts.
Regarding the second part, we are a co-founder of the IT best practices open source project, which collects and curates best practice rules, with primary emphasis on security hardening. This project is in its infancy, but already has collected a few hundred rules from NIST STIGs. Our plan is to incorporate more STIGs, and additional rules from other freely available sources like the Lynis project.
If you are one of those many organizations which have trouble staying in compliance, then you need to look into the Assimilation System Management Suite. If you are a security expert, you need to come alongside and help evaluate and critique security rules at the IT Best Practices project and help lead the charge to improve the state of security in the world.

Please note: I reserve the right to delete comments that are offensive or off-topic.