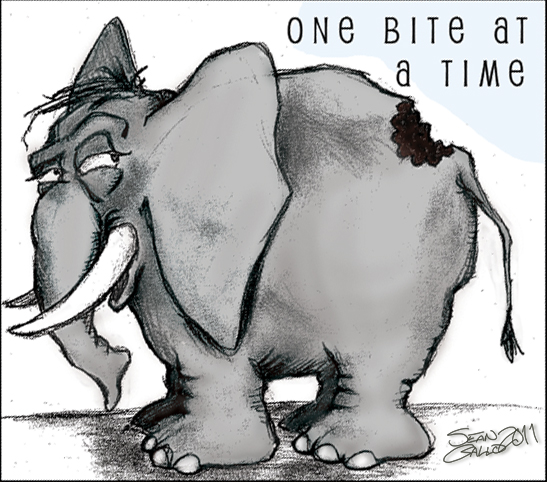
Even good security rules need to grow

Although Linux systems are by-and-large more secure than many other systems, they still need to be administered intelligently. Stupid configurations often lead to unfortunate results. According to Akamai: “As the number of Linux environments has grown, the potential opportunity and rewards for criminals has also grown”. As part of the IT best practices project, I’ve recently added a rule which disallows password authentication over ssh. This blog post explains this, and why people who manage Linux systems should care.